Transforming Mainframe Operations with Automation, AIOps & Secure Modernization
We help enterprises modernize legacy systems, infuse AI-driven observability, automate operational tasks, and harden risk & compliance across the mainframe estate.
Transforming Mainframe Operations with Automation, AIOps & Secure Modernization
We help enterprises modernize legacy systems, infuse AI-driven observability, automate operational tasks, and harden risk & compliance across the mainframe estate.
Consolidated Operations Dashboard
Single unified view for mainframe operations by integrating ITSM, legacy monitors, and other tools into one console.
Unified Operational Visibility
Centralize operational data from mainframe and enterprise systems into a single, authoritative control plane.
Integration across ITSM, monitoring, and legacy platforms
Unified operational context across environments
Elimination of tool fragmentation and data silos
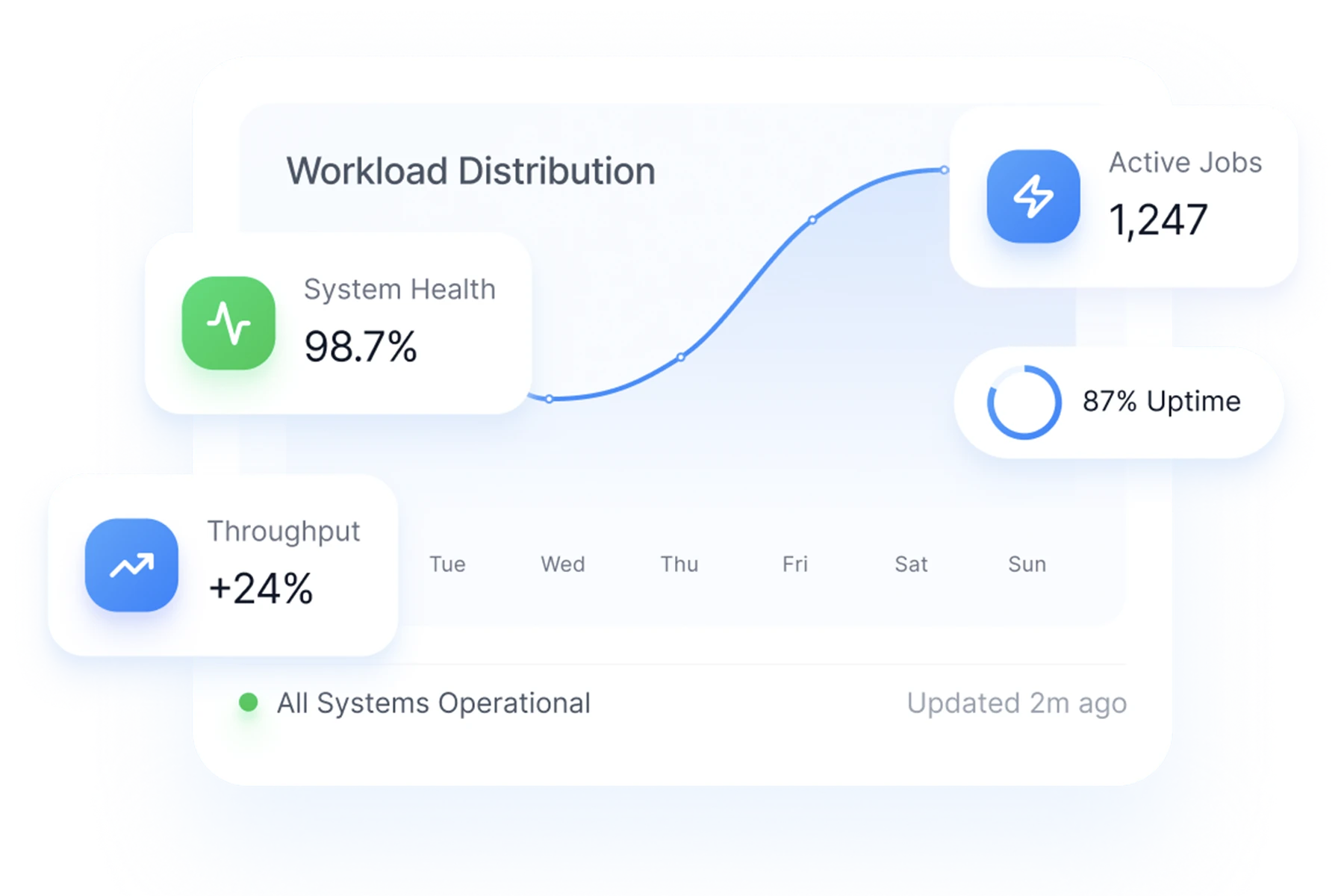
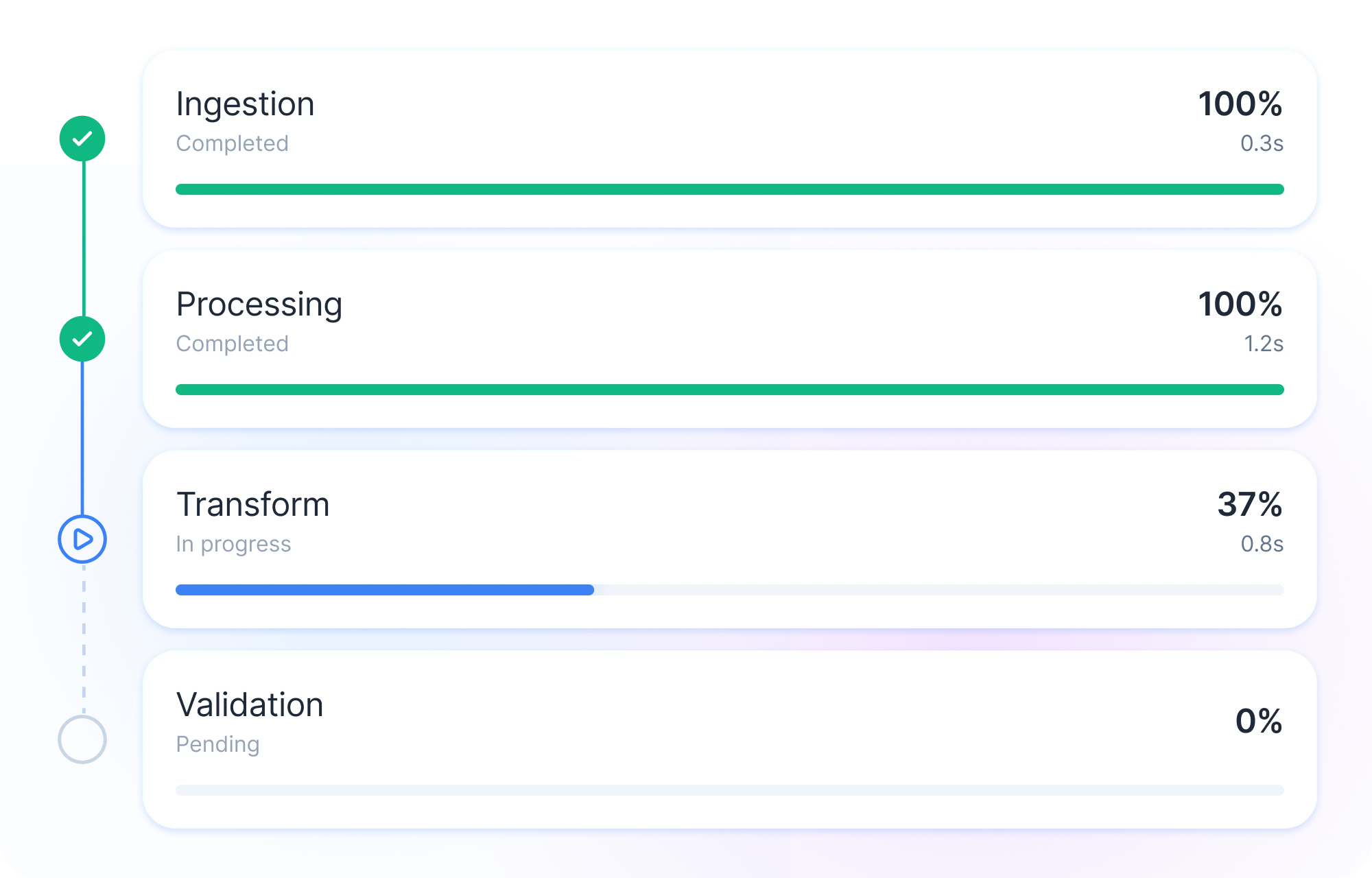
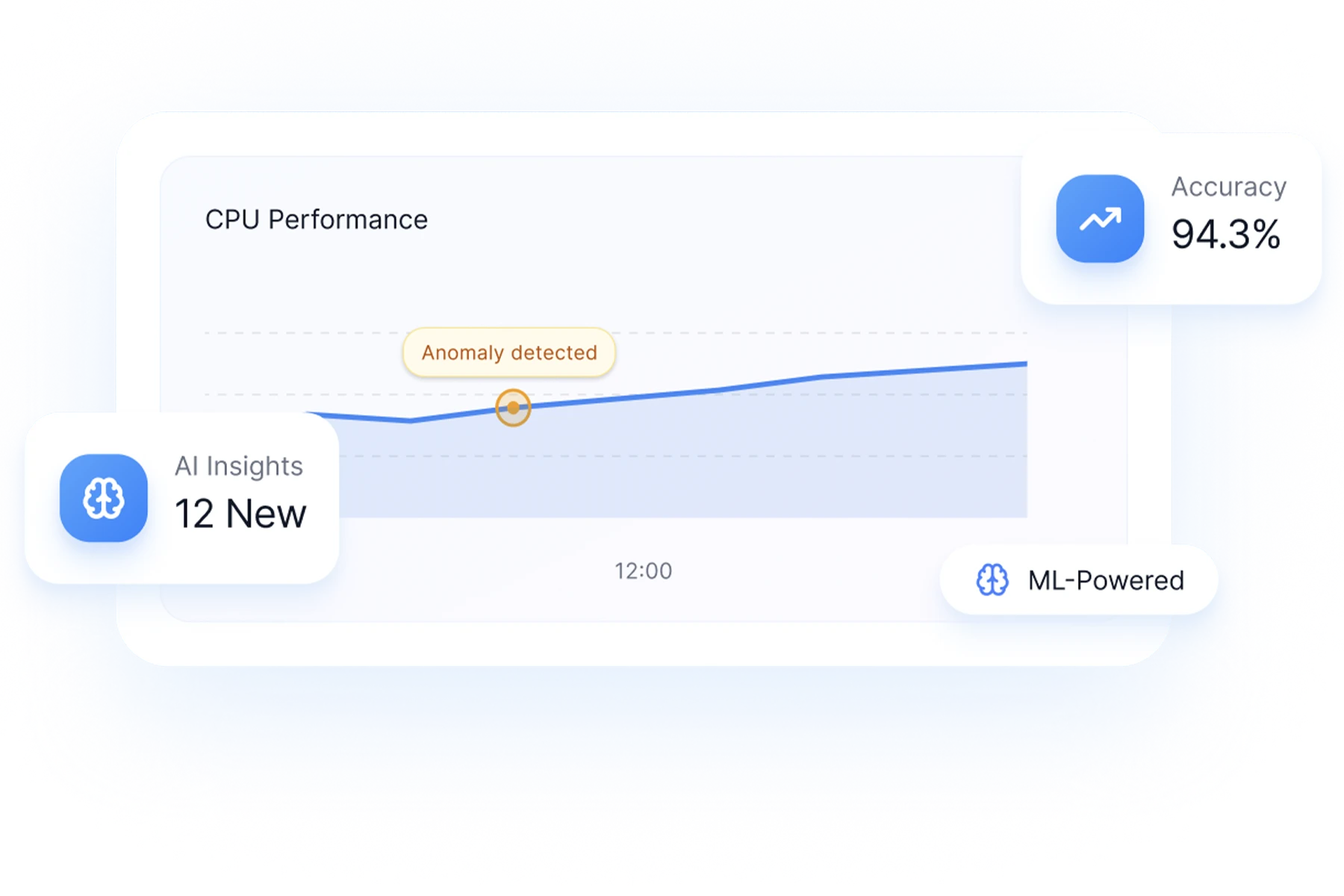
Real-Time Performance Oversight
Monitor workloads, system health, and execution pipelines in real time with proactive intelligence.
Live workload and performance metrics
Predictive analytics and anomaly detection
SLA, throughput, and capacity visibility
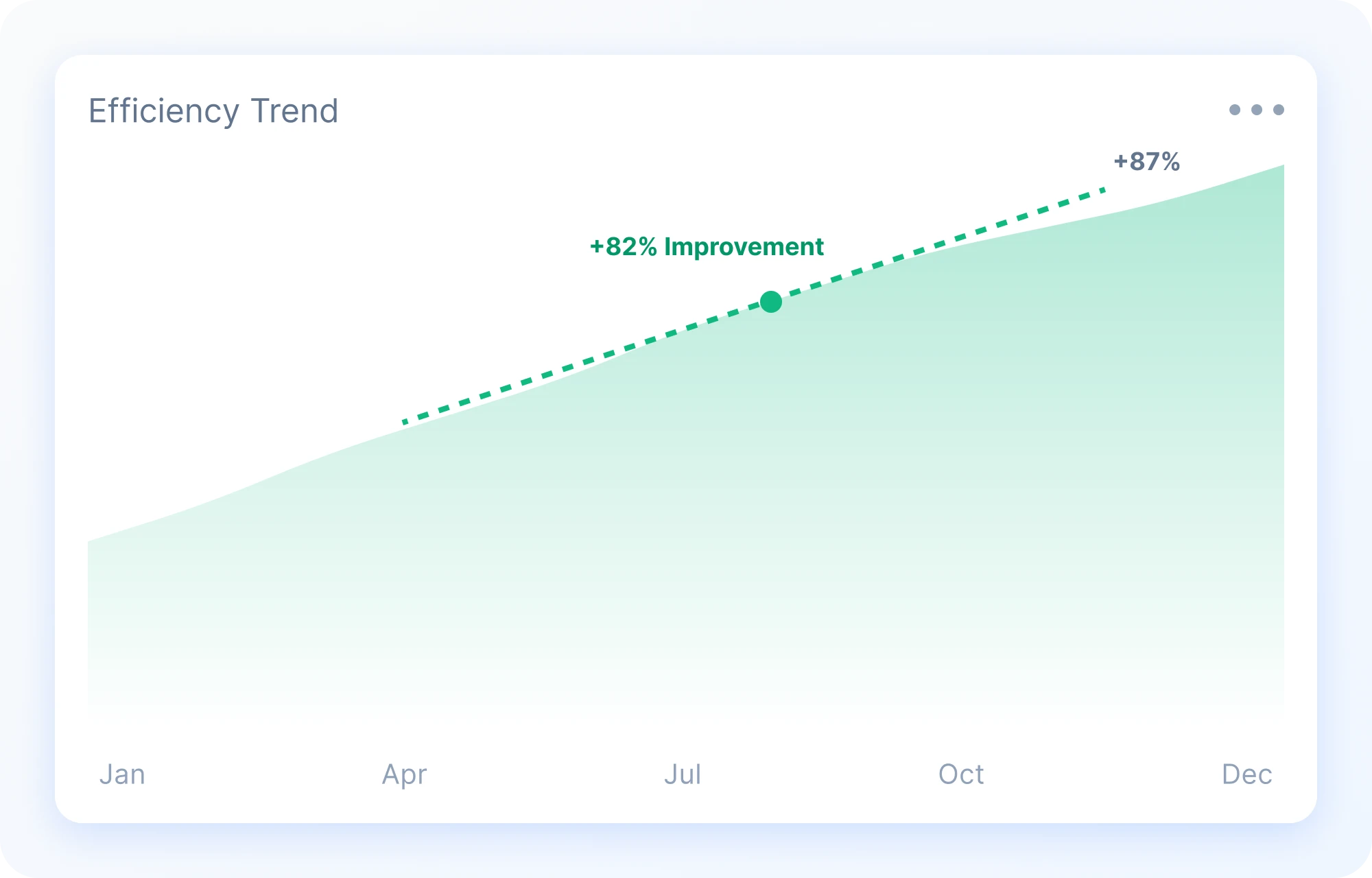
Operational Efficiency at Scale
Enable faster decision-making and optimized resource utilization through actionable insights.
Reduced MTTR and operational overhead
Improved system reliability and uptime
Data-driven operational governance
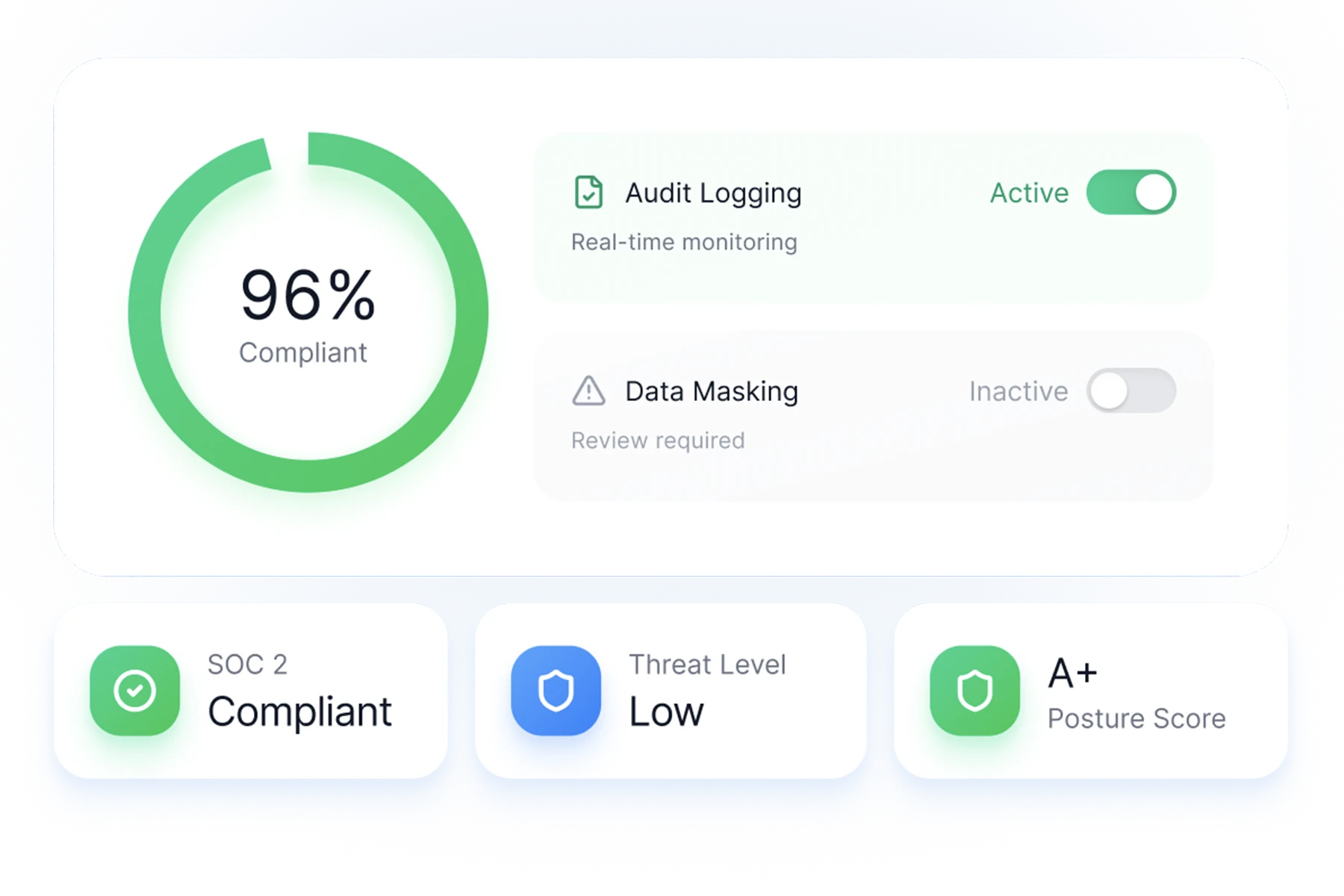
Security & Compliance Automation
Automate collection of security baseline data, generate compliance dashboards, and auto-produce regulator-ready reports.
Automated Security Baselines
Continuously assess security posture across mainframe environments against regulatory and internal standards.
Alignment with SOC 2, ISO 27001, PCI-DSS, and internal policies
Automated baseline assessment
Reduced manual compliance effort

Continuous Risk Intelligence
Identify vulnerabilities, misconfigurations, and policy deviations through real-time monitoring and risk scoring.
Threat-level indicators and prioritization
Policy violation detection
Security posture trend analysis
Audit-Ready Compliance Reporting
Generate regulator-ready reports and evidence artifacts automatically, ensuring continuous audit readiness.
Automated audit documentation
Historical compliance traceability
One-click report generation
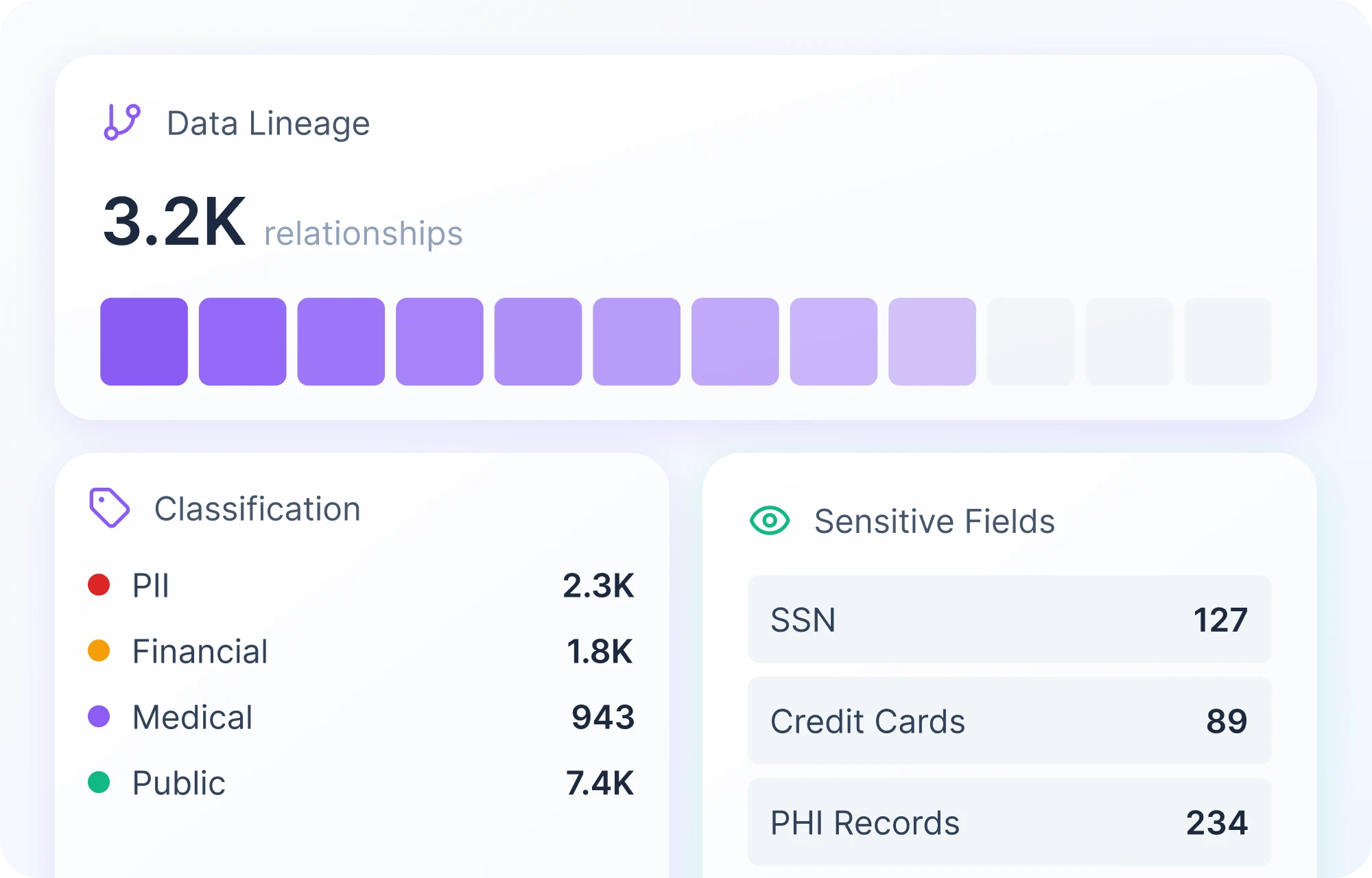
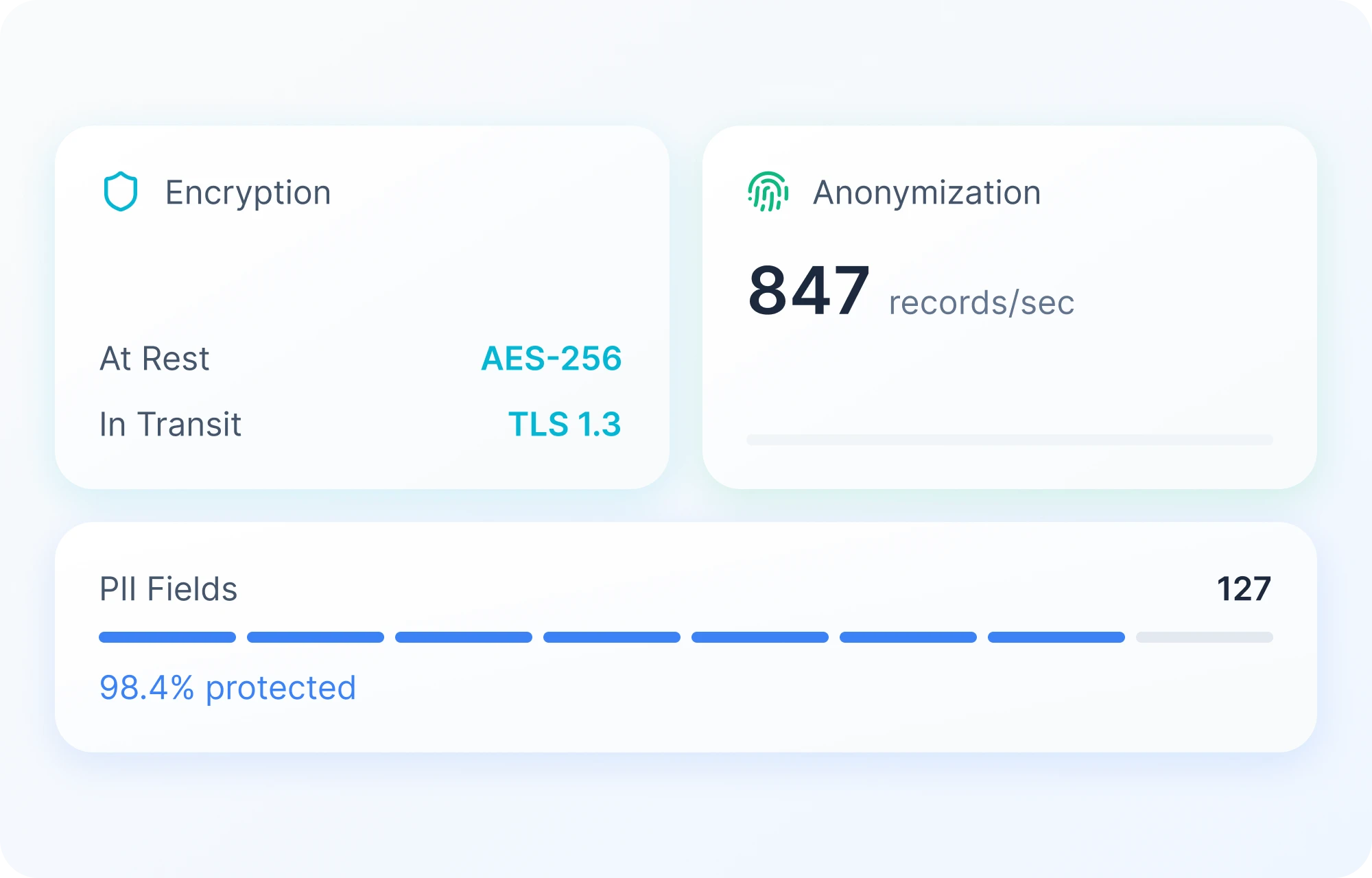
Data Masking & Privacy Protection
Protect sensitive mainframe data across non-production environments by automating the discovery and de-identification of PII and sensitive business information.
Intelligent Data Discovery
Automatically discover, classify, and contextualize sensitive data across mainframe and downstream environments.
Detection of PII, PHI, and sensitive business data
Automated classification and tagging
Cross-environment data mapping
Policy-Driven Data Masking
Protect sensitive data using persistent, policy-based masking while preserving system functionality and analytical value.
Static and dynamic masking models
Role- and context-based masking policies
Non-disruptive workflow integration
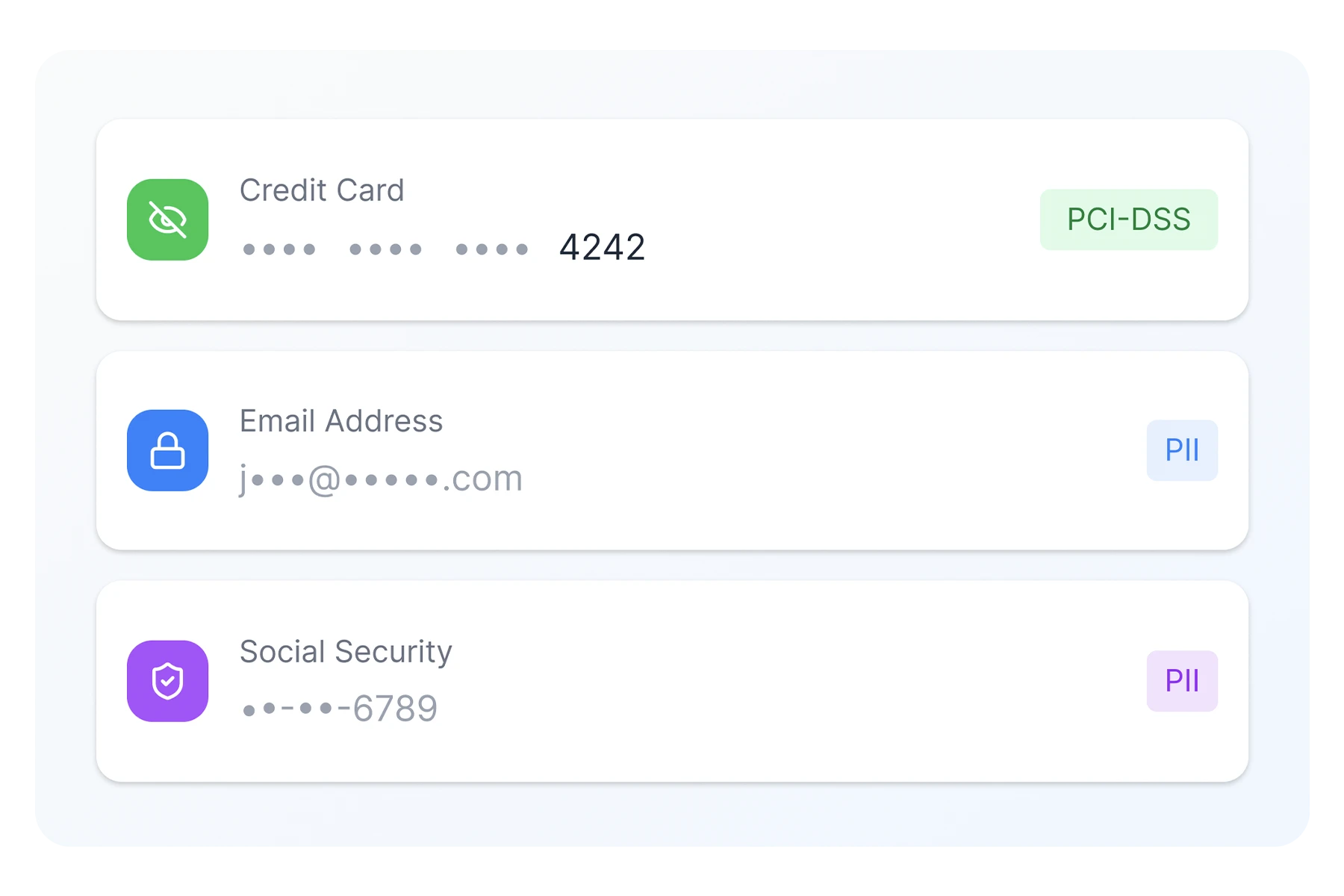
Privacy-Centric Data Architecture
Embed privacy controls into data workflows to minimize breach risk and ensure regulatory compliance.
Alignment with GDPR and global privacy regulations
Reduced exposure in non-production environments
Strengthened enterprise data governance
Purpose-built Solutions for Modern Mainframe Operations
Frequently Asked Questions
The platform supports mapping controls to major regulatory and industry frameworks including NIST, ISO 27001, SOC 2, PCI DSS, CIS, and banking-specific regulatory standards. Custom frameworks can also be configured to meet internal or regional compliance requirements.
The platform integrates with enterprise and mainframe systems to collect control evidence automatically where possible. Evidence can also be uploaded manually and tracked centrally, ensuring a complete and auditable trail.
Yes. The solution is designed to operate within mainframe-centric environments and can integrate with relevant systems to support control tracking, evidence collection, and compliance reporting.
Role-based access controls ensure that users only see information relevant to their role. All activity is logged to maintain a full audit trail.
Unlike spreadsheet-driven processes, the platform provides centralized control visibility, automated evidence tracking, compliance dashboards, and continuous monitoring — eliminating manual fragmentation and version control risks.
Unlike spreadsheet-driven processes, the platform provides centralized control visibility, automated evidence tracking, compliance dashboards, and continuous monitoring — eliminating manual fragmentation and version control risks.
Get Started Right Away
Book a Free Consultation with our Team

